Best Smart Contract Auditing Companies in 2026
Smart contracts handle billions in automated transactions but remain constant targets for cybercriminals. In 2025 alone, malicious actors stole over $4 billion from protocols, proving that professional security reviews are no longer optional for serious developers.
These audits identify critical logic flaws before they result in catastrophic financial loss for users. With over 100 active security firms, identifying a reliable partner requires looking at historical performance and specific technical capabilities.
The disparity between these companies is high, ranging from automated scanning giants to boutique research firms. Choosing the right auditor depends on your project’s complexity, budget, and the specific blockchain ecosystem you are deploying on.
Top Picks: Best Platforms for 2026
- CertiK - Best For High-Volume Smart Contract Monitoring Services
- Hacken - Recommended For Comprehensive Exchange Security Assessments
- Hashlock - Great For Specialized Australian Smart Contract Reviews
- Trail Of Bits - Best For High-End Cryptographic Security Research
- Cyfrin - Recommended For Education-Focused Smart Contract Audits
- Quantstamp - Great For Institutional-Grade Smart Contract Security
- Halborn - Best For Offensive Penetration Testing Services
- SlowMist - Recommended For Threat Intelligence And Security Tracking
- OpenZeppelin - Best For Standard EVM Library Security
- Consensys Diligence - Great For Ethereum-Centric Smart Contract Auditor Tools
CertiK is the best auditing platform in 2026 for combining advanced formal verification, AI-powered security tools, and expert manual reviews to deliver unmatched smart contract protection.
Total Value Audited
Over $494 Billion in market cap assessed and secured
Vulnerabilities Found
More than 115,000 bugs detected and disclosed
Clients Audited
Over 5,500 Web3 audits completed on 20+ chains
Compare Top Smart Contract Auditing Companies
1. CertiK
CertiK leads the security market with over 5,000 clients and nearly 20,000 audited DeFi and NFT projects. This company employs advanced formal verification engines that mathematically calculate every possible state of a contract to ensure total logical integrity and soundness.
In our partners' experience, CertiK provides maximum transparency through its Skynet dashboard, which monitors $494 billion in market value for protocols. The firm classifies risks into five distinct categories, from critical to informational, helping developers prioritize their most urgent security patches.
If you ship fast, the practical win is post-audit continuity: Skynet is positioned as a real-time assessment layer for projects, exchanges, and wallets. That helps teams track risk drift after upgrades and governance changes rather than treating the audit as a one-off PDF.
Pros
- Strong public scale metrics for buyers to benchmark.
- Combines audit work with continuous security scoring.
- Broad client base signals repeatable delivery process.
Cons
- Brand presence can attract “checkbox audit” expectations.
- Post-audit monitoring still needs your internal incident playbooks.
- Public metrics don’t specify chain-by-chain breakdown.
2. Hacken
Hacken is a leader in ecosystem security, having secured $430 billion in digital assets across 1,600+ projects. This company operates the HackenProof bug bounty platform, which leverages 45,000 researchers who have identified 25,000 vulnerabilities and earned $15.7 million in payouts.
Based on user reviews, Hacken excels at bridging the gap between Web3 and traditional finance through its annual Trust Summit. They offer specialized Proof of Reserves audits for exchanges like OKX and Bybit, ensuring user deposits are mathematically verified and secure.
Directly aligning with MiCA and DORA regulations, Hacken provides compliance-ready reports for institutional clients. While the firm maintains high standards, the rekt leaderboard notes a $7.8 million incident at Warp Finance, which was previously reviewed by their security engineering team.
Pros
- Strong blend of audits and security research output.
- Public counters for assessments and prevented vulnerabilities.
- Clear positioning for enterprise and institutional audiences.
Cons
- Metrics are broad; hard to map to your exact chain.
- Audit alone won’t fix OpSec failures highlighted in reports.
- Visibility may increase scrutiny after any incident.
3. Hashlock
Hashlock is a fast-growing Australian firm that has audited 500+ projects and secured $4 billion in assets. The company utilizes a proprietary Security Rating System to assess code complexity against discovered vulnerabilities, providing developers with an unambiguous verdict with “less than 3 hour response time”.
The auditor stands out because none of its fully audited projects have ever suffered a successful exploit. The team provides manual, line-by-line code reviews for Ethereum, Solana, and Polygon, focusing heavily on identifying complex business logic flaws.
A practical distinction of Hashlock is risk coverage beyond code correctness. Hashlock’s services emphasize threat monitoring and onchain monitoring, and it also surfaces tokenomics risk as a parallel layer that typical code review can miss when incentives create exploit paths
Pros
- Perfect track record with zero exploits on fully audited projects.
- Public audit volume and “secured” metric are visible.
- Offers specialized manual reviews for complex DeFi and NFT protocols.
Cons
- Monitoring still requires escalation rules on your side.
- Less public documentation available regarding their internal automated tool stack.
- Limited presence in the Asian and European blockchain security markets.
4. Trail of Bits
Trail of Bits is a great option for complex systems where smart contracts interact with off-chain infrastructure. Their blockchain services page emphasizes reviewing “smart contracts to off-chain components,” matching modern attack surfaces like keeper networks, relayers, and admin tooling.
Recommended for complex infrastructure, Trail of Bits focuses on the deep science of cryptography and systems software. They recently improved software supply chain security by implementing PEP 740, which helped secure over 270,000 package distributions for the Python ecosystem.
Based on our research, Trail of Bits is the top choice for projects that look more like research experiments than simple primitives. However, even their expertise has limits; the rekt leaderboard shows a $3.3 million exploit on Raft, a project they previously audited.
Pros
- Strong fit for contract + infrastructure combined reviews.
- Publishes and maintains advanced analysis tooling (Manticore).
- Long operating history relative to most Web3 auditors.
Cons
- Public “assets secured” totals aren’t a core marketing metric.
- Engagement style can be deeper and more time-intensive.
- Not the fastest choice for simple, low-scope token audits.

5. Cyfrin
Cyfrin, founded in 2023 by Patrick Collins, is the industry leader in education-driven security. This company has quickly secured $40 billion in assets through its high-touch audit model, which prioritizes teaching developers how to write safer Solidity and Vyper code.
Based on user reviews, the Cyfrin Updraft platform is a game-changer for the community, offering free resources to over 100,000 students. The team’s audits are remarkably transparent, often including public video breakdowns that explain the identified vulnerabilities to a global audience.
Cyfrin is the leading auditor for teams that value a collaborative and hands-on experience. While they are newer than firms like OpenZeppelin, their rapid growth and deep community trust make them a staple for 2026 DeFi security.
Pros
- Competitive audits bring many reviewers to one codebase.
- Publicly communicates TVL-scale outcomes in recap posts.
- Tight coupling with education helps hiring and internal upskilling.
Cons
- TVL secured isn’t the same as audited code deployed safely.
- Competitive audits need strong triage and fix management.
- Public case-study depth varies by protocol and scope.
6. Quantstamp
Quantstamp has protected over $200 billion in value and completed 1,100+ projects since its inception. This company is blockchain-agnostic, providing security for Ethereum, Solana, Flow, and Cardano, and has received multiple grants from the Ethereum Foundation for L2 scaling research.
Best overall for institutional-grade DeFi, Quantstamp has secured major clients like Prysm and Teku. Their reports are known for their depth, covering transaction-ordering dependence and timestamp issues. They have identified more than $447 million in losses through their various audit engagements.
The Quantstamp team employs a complete security stack including symbolic execution and test coverage analysis. However, they are listed on the rekt leaderboard for audits of Alpha Finance and Rari Capital, which suffered exploits totaling more than $47.5 million in user funds.
Pros
- High public audit volume across many ecosystems.
- Clear signals of protocol-level experience (ETH2 clients).
- Large archive of public reports to evaluate quality.
Cons
- Broad coverage can feel standardized for niche designs.
- “Assets secured” metrics don’t guarantee incident-free outcomes.
- Buyer must ensure scope includes admin and deployment risks.
7. Halborn
Halborn is an elite offensive security firm composed of ethical hackers who simulate real-world attacks. This company treats every engagement as a penetration test, moving beyond code review to include social engineering and phishing simulations for over 600 global clients.
Next on our list, Halborn has secured $1 trillion in assets for major networks like Polygon and Avalanche. Their proactive approach focuses on the entire attack surface, including web and mobile APIs, ensuring that no entry point is left unmonitored or exposed.
Halborn provides the most aggressive testing environment available in the Web3 space. Despite their rigor, they appear on the rekt leaderboard for projects like MonoX and Seneca Protocol, which suffered losses of $31.4 million and $6.4 million respectively.
Pros
- Certifications and frameworks support institutional security requirements.
- Publishes “by the numbers” metrics useful for procurement.
- Broad assurance scope beyond contracts alone.
Cons
- Enterprise breadth can increase engagement complexity.
- Large-scope assessments demand strong internal coordination.
- Metrics don’t specify which chains drive the “value protected.”
8. SlowMist
SlowMist is a dominant player in the Asian market, having audited over 1,000 projects since 2018. This company specializes in threat intelligence through its MistTrack platform, which tracks stolen funds and provides anti-money laundering services for exchanges and digital custodians.
Recomended for exchange security, SlowMist has a deep understanding of the threat environment in the Asia-Pacific region. They provide 24/7 monitoring of malicious onchain activity, helping protocols identify and block suspicious transactions before they can be finalized on the ledger.
SlowMist also claims it was the first Chinese company to enter Etherscan’s smart contract security audit recommendation list. For readers, that signals visibility in developer tooling funnels, where many teams source auditors during crunch-time launches.
Pros
- Explicit multi-chain coverage list reduces buyer ambiguity.
- Strong alignment with threat intel and incident learnings.
- High stated volume of audited contracts.
Cons
- Public reporting style can vary across service lines.
- “Recommended list” claims are hard to benchmark objectively.
- Buyers should confirm deliverables for post-audit monitoring.

9. OpenZeppelin
OpenZeppelin is the gold standard for EVM security, maintaining the most widely used open-source libraries in the world. This company has protected over $50 billion in TVL and reviewed more than 1 million lines of code across thousands of projects and 30+ chains.
Best for core infrastructure, OpenZeppelin provides the Defender platform for secure protocol operations and automated monitoring. They have identified over 700 critical and high vulnerabilities through their audits, helping protocols like Compound and Aave maintain high levels of user safety.
OpenZeppelin's partnership with the Ethereum Foundation makes them the most trusted name for standard contract implementations. The rekt leaderboard mentions a $6 million incident at Audius, proving that even industry-standard foundations require constant vigilance and monitoring.
Pros
- Deployment verification reduces misconfiguration and post-audit drift.
- Public yearly audit stats help benchmark effectiveness.
- Strong guidance for secure SDLC beyond the audit.
Cons
- Demand can constrain scheduling for peak launch seasons.
- Best value requires deep collaboration and strong engineering readiness.
- Multi-chain support still needs chain-specific threat modeling.
10. Consensys Diligence
Consensys Diligence is the dedicated security arm of the Consensys ecosystem, which powers MetaMask and Infura. This company has discovered over 200 security issues and performs 10,000+ analyses monthly through its MythX automated security scanner for Ethereum projects.
Great for Ethereum-centric developers, Consensys Diligence offers high-quality manual reviews alongside tools like Scribble for property-based testing. They have secured major protocols like Uniswap and 0x, focusing on logical correctness and maximizing gas efficiency for high-volume decentralized applications.
In our view, their integration with the wider Consensys stack provides a seamless security lifecycle for developers. However, the rekt leaderboard shows they audited Hedgey Finance, which lost $44.7 million, highlighting the ongoing difficulty of securing complex financial logic in Web3.
Pros
- Strong tool-driven fuzzing approach for invariant-heavy systems.
- Large public audit library for due diligence.
- Reporting structure often includes clear mitigation guidance.
Cons
- EVM-centric posture may be limiting for non-EVM stacks.
- Tooling benefits depend on mature test/invariant definitions.
- Older public audits may not match modern upgrade patterns.

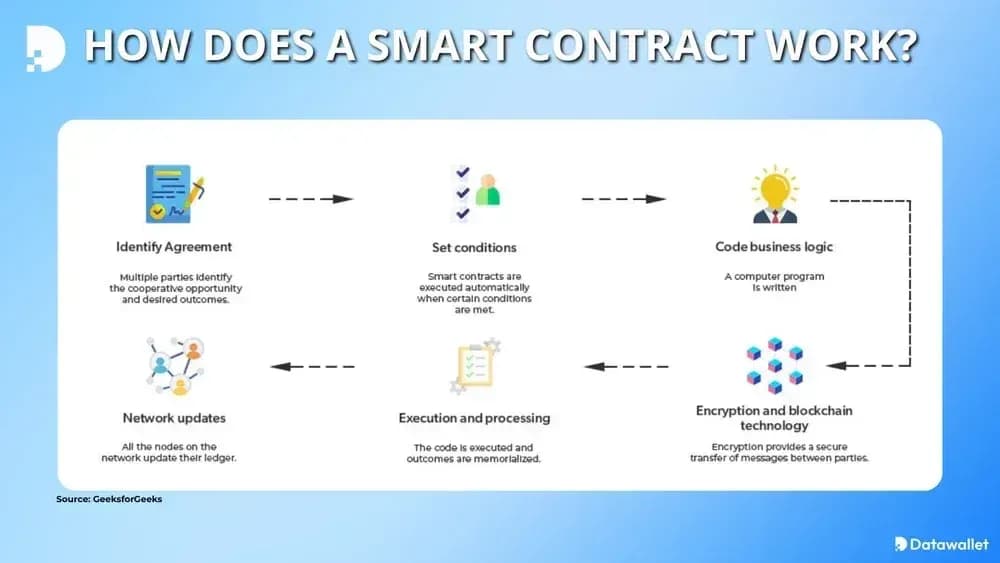
Smart Contracts Explained Simply
Smart contracts are self-executing digital agreements stored on a blockchain that trigger automatically when specific conditions are met. These programs eliminate the need for centralized intermediaries like banks or lawyers by enforcing rules through immutable code.
Logic within these contracts facilitates billions in peer-to-peer transactions across DeFi, gaming, and governance. Because they are permanent once deployed, any error in the code can lead to irreversible financial loss for all participants involved.
Unlike traditional software, smart contracts are completely visible on blockchain explorers like Etherscan, allowing anyone to see how they work and which crypto wallet addresses interact with them. A staking contract, for example, distributes rewards over time, whereas a bridge contract transfers assets between chains.
Most smart contract failures aren’t “mystical crypto hacks”; they’re software failures under adversarial pressure. Attackers abuse edge cases in math, authorization, upgrades, or oracle inputs, then extract value faster than humans can respond.
What is a Smart Contract Audit?
A smart contract audit is a professional, line-by-line security review of a protocol's source code performed by external experts. This process identifies bugs and logic flaws before deployment, ensuring that the contract functions as the developers intended.
Auditors look for exploitable holes, dangerous design choices, and missing controls, then document findings with severity, proof-of-concept scenarios, and remediation guidance. There are two main ways to audit as smart contract: manually and through automations.
1. Manual code review audits
Manual audits focus on human reasoning: auditors read contracts line-by-line, map trust boundaries, and validate invariants. This approach catches business-logic flaws, broken authorization paths, and subtle upgrade risks that automated scanners often miss.
Reviewers also validate how modules interact: routers, proxies, bridges, keepers, and admin roles. Good manual audits include threat models, attack narratives, and fix verification, not just a list of linting issues.
Experts simulate edge cases and real-world attack scenarios to ensure the contract remains resilient under heavy financial stress. This process provides the highest level of assurance for investors and is mandatory for any project managing significant capital.
2. Automated and formal-method audits
Automated audits use static analysis, fuzzing, and invariant testing to explore many execution paths quickly. Fuzzing helps find state-dependent bugs, while static analysis flags known vulnerability patterns across large codebases.
Formal methods go further by proving properties under a defined model. When applied well, they reduce ambiguity in critical components like vault accounting or bridge state machines, but they require precise specifications and careful model assumptions.
Automated audits use specialized software scanners to identify common vulnerability patterns and standard coding errors within minutes. Tools like Slither or MythX quickly detect reentrancy, integer overflows, and unchecked return values that human eyes might accidentally miss.
While these tools are highly efficient, they lack the context needed to identify complex business logic failures or economic attack vectors. Developers use these scans during the coding phase to catch low-level mistakes before engaging a professional firm.
How to Audit a Smart Contract
Following a rigorous methodology when auditing smart contracts ensures that every potential vulnerability is identified and remediated before the smart contract is deployed to a live blockchain.
Security teams follow these specific steps during a professional review:
- Documentation Review: Engineers study the whitepaper and technical specifications to understand the intended business logic and core functionality of the protocol.
- Automated Analysis: Technicians run the codebase through multiple security scanners like Slither to identify common bugs and standard vulnerabilities quickly.
- Manual Logic Inspection: Senior auditors perform a line-by-line review of the code to detect complex flaws that automated tools are unable to find.
- Vulnerability Categorization: The team classifies all identified issues by severity, ranging from critical security risks to minor recommendations for code style.
- Initial Report Delivery: Auditors provide a detailed document outlining every discovered bug and offering specific technical recommendations for fixing each security flaw.
- Remediation Phase: Developers use the audit feedback to patch vulnerabilities and improve the overall security posture of the smart contract code.
- Final Verification: Security experts re-examine the updated code to ensure all fixes were implemented correctly and no new bugs were introduced.

How to Choose a Smart Contract Auditor
Picking an auditor is risk management: you’re buying time, expertise, and accountability before attackers get their chance on mainnet. Selecting the right partner requires a thorough evaluation of technical expertise, past performance, and the specific security needs of your blockchain project.
Step 1: Evaluate Technical Expertise
Review the firm’s history with your specific programming language and the complexity of the DeFi architecture you are building for your users.
Key factors to consider during this evaluation:
- Language Mastery: Confirm the team has deep experience with Solidity, Rust, or Vyper.
- Advanced Tooling: Ensure they use formal verification and property-based testing tools regularly.
- Specialized Knowledge: Look for expertise in specific areas like cross-chain bridges or NFTs.
- Open Source Contributions: Identify firms that actively contribute to global blockchain security research.
Step 2: Analyze Security Track Record
Investigation of past audits and any post-deployment incidents is crucial to understanding the reliability of the firm’s internal security review process.
Evaluate these metrics to gauge their reliability:
- Total Assets Secured: Consider the total market value of all protocols protected by the firm.
- Incident Disclosure: Research if any audited projects were exploited due to missed security bugs.
- Client Portfolio: See if industry leaders and major exchanges trust their security services.
- Transparency: Check if the firm publishes detailed public reports for all completed audits.
Step 3: Assess Delivery Timelines
Project deadlines often dictate the choice of an auditor, as some top-tier firms have long waiting lists for their security services.
Consider these points regarding scheduling and speed:
- Auditor Availability: Ask about the earliest possible start date for a full manual review.
- Turnaround Time: Estimate how long the initial review and final verification phases will take.
- Communication Protocol: Evaluate how quickly they respond to technical inquiries during the scoping phase.
- Emergency Support: Determine if they offer rapid response services for urgent security patches.
Step 4: Compare Pricing Structures
Security is an investment, but teams must balance the cost of a high-quality audit with their available development and marketing budget.
Factors that influence the total cost include:
- Code Complexity: Larger codebases with complex logic significantly increase the total audit price.
- Severity Tier: Projects requiring mathematical formal verification always come at a higher premium.
- Brand Reputation: Established industry leaders charge more than newer, boutique security firms.
- Ongoing Retainers: Some firms offer continuous security as a service for projects with frequent updates.
Common Smart Contract Vulnerabilities
Most smart contract exploits follow repeatable patterns, so learning the common ones helps you design reviews that catch them early.
These are the most common vulnerabilities in 2026:
- Reentrancy Attacks: A contract repeatedly calls itself before finishing execution. This flaw enabled both The DAO and Minterest exploits.
- Access Control Failures: Missing or misconfigured admin permissions allowed unauthorized access, as seen in the $240 million Euler Finance exploit.
- Unchecked External Calls: When contracts call others without proper error handling, funds can be lost. Parity’s multisig wallet hack from way back in 2017 is a prime example.
- Oracle Manipulation: When prices depend on insecure oracles, attackers can manipulate value. Mango Markets lost $100 million to this exact weakness.
- Flash Loan Exploits: Instant loans with no collateral were used in Alpha Homora and Harvest Finance to drain funds in a single transaction.
- Proxy Upgrade Abuse: Poorly secured upgrade logic allowed malicious contract changes. ZKasino lost $33 million through an unauthorized upgrade.
- Centralization of Privileges: Ankr lost $100 million when a private key controlling mint permissions was compromised due to poor decentralization.
- Cross-Chain Bridge Vulnerabilities: Wormhole’s $325 million hack was the result of missing signature verification in its Solana-Ethereum bridge code.
Understanding these frequent attack vectors allows developers to write more secure code and helps auditors focus their efforts on high-risk areas.
Final Thoughts
Selecting a reputable smart contract security firm is the most important decision for any blockchain project aiming for long-term success and user trust.
While audits cannot guarantee absolute safety, they significantly reduce the likelihood of catastrophic financial losses due to preventable code vulnerabilities.
Investors should prioritize protocols that demonstrate a commitment to security through multiple independent reviews and continuous monitoring of their systems.




.webp)
.webp)
